In this post, I will show you 3 ways to block USB drives using Intune. There is always a security risk when USB storage drive access is allowed on corporate devices. Users can download sensitive data on external drives, which, if misused, could affect the organization’s reputation.
Blocking removable storage devices on company-owned devices is essential for preventing potential security breaches. By doing so, you can ensure that confidential information is not saved or copied to personal storage devices, thereby safeguarding sensitive data and maintaining a secure working environment.
You can use Device restriction template or Attack surface reduction policy to block USB drives on Windows 10 and Windows 11 devices. Another option to block USB drives is to use Intune device remediations.
Contents
Method 1: Using Device Restrictions Intune Template
- Sign in to the Intune admin center > Devices > Configuration > Create > New Policy.
- Select Platform as Windows 10 and later
- Profile type as Settings Catalog
- Click on the Create button.
- Basics Tab – Provide a Name and Description of the Policy and Click on Next.
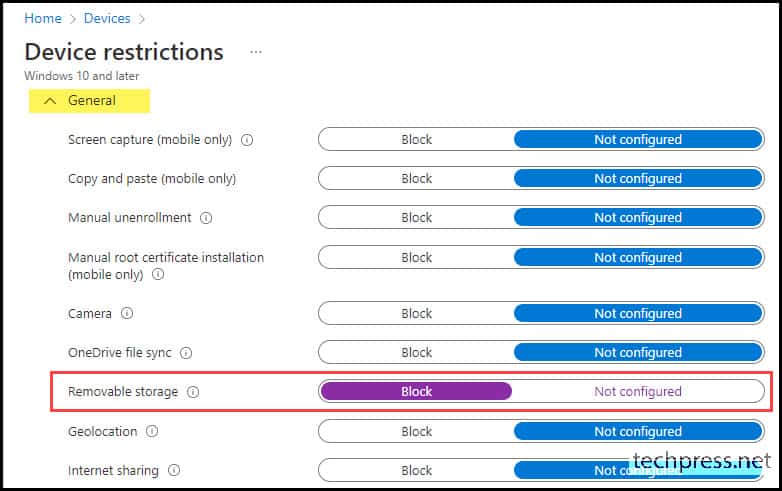
- Configuration settings – Scroll down and Expand the General category settings. Look for Removable storage and use the toggle switch to select Block.
Method 2: Attack Surface Reduction Policy
- Sign in to the Intune admin center > Endpoint security > Attack surface reduction.
- Click on + Create Policy.
- Platform: Windows.
- Profile: Device Control.
- Basics Tab: Provide a Name and Description of the Policy and Click on Next.
- Configuration settings Tab: Scroll down to find a Removable Disk Deny Write Access setting under Storage. Use the drop-down and select Enabled. Click on Next.
- Scope tags: Click on Next.
- Assignments: Click on Add groups and select an Entra security group containing Windows devices.
Method 3: Using Intune Device Remediations
You can leverage Intune Device Remediations to block USB drives. For a detailed, step-by-step guide, please refer to the link: Block USB Drives access on Windows using Intune remediations.
Sync Intune Policies
The device check-in process might not begin immediately. If you’re testing this policy on a test device, you can manually kickstart the Intune sync either from the device itself or remotely through the Intune admin center.
Alternatively, you can use PowerShell to force the Intune sync on Windows devices. Another way to trigger the Intune device check-in process is by restarting the device.
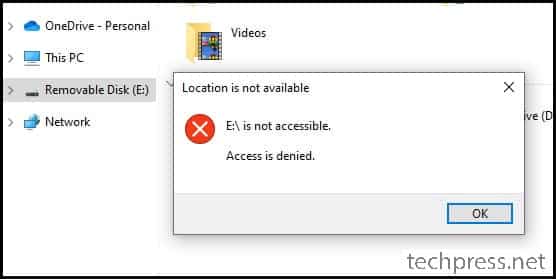
End User Experience
Once this policy has been successfully applied to target devices, Users will not be able to access USB drives and will get an error: Location is not available, <drive letter:>\ is not accessible. Access is denied.
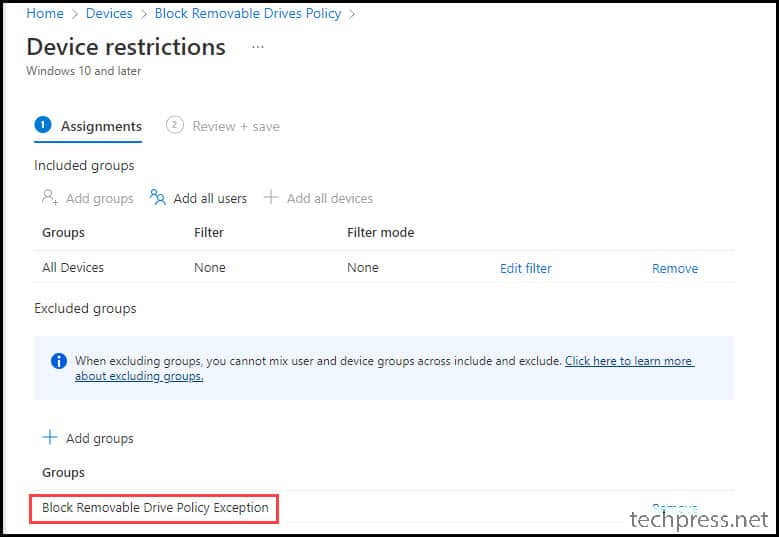
USB Drive Block Policy Exclusions
There can be certain devices or users where you do not want to block USB drivers. For those users or devices, you can create a new Entra security group and add this group in Exclusions section of the Intune policy.
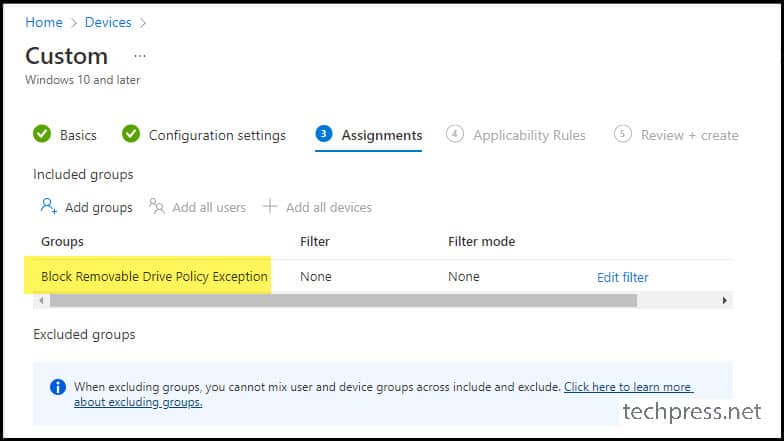
Below screenshot shows an Entra security group: Block Removable Drive Policy Exception is added to the Excluded group section.
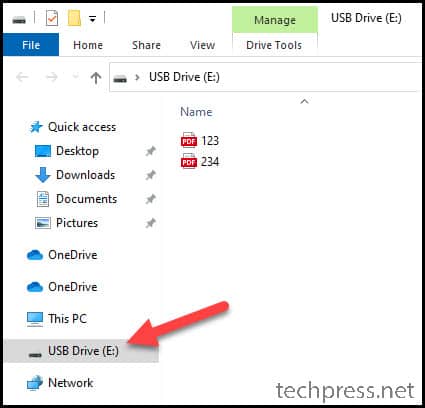
Below screenshot is from a device which was added to the Block Removable Drive Policy Exception Entra security group to test is the exclusion is working fine. As we can see, the USB drive is accessible.
USB Drive Block Policy Exclusions: Option 2
There is another way to create USB drive block policy exclusions which utilizes OMA-URI settings. Let’s check the steps:
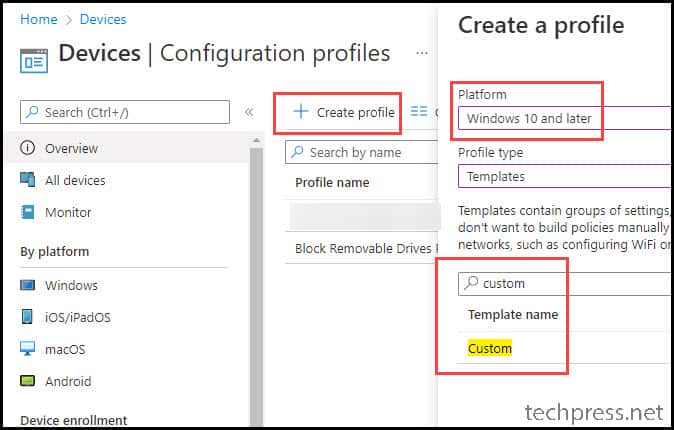
- Intune admin center > Devices > Configuration > Create > New Policy.
- Platform: Windows 10 and later
- Profile Type: Templates
- Template Name: Custom
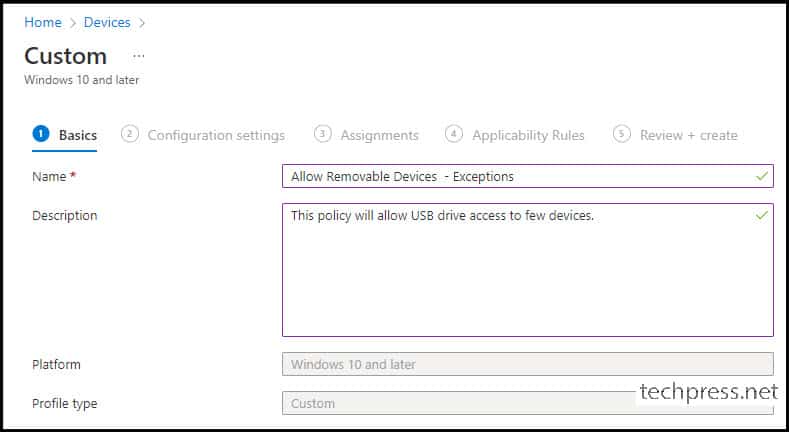
- Basics Tab: Provide a Name and Description of the policy.
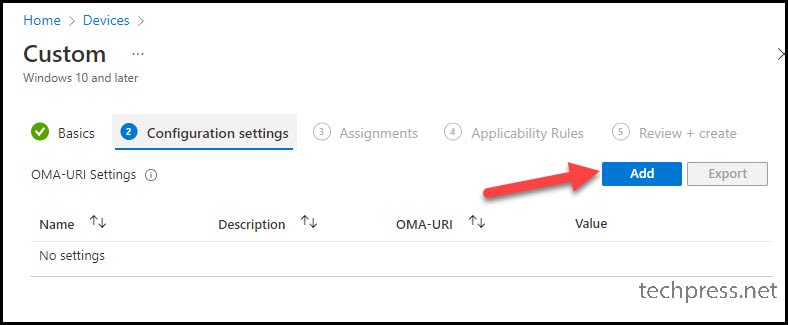
- Configuration Settings: Click on Add button to add OMA-URL settings.
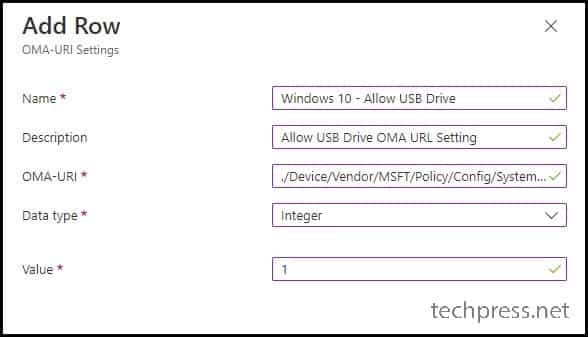
- Provide below OMA-URI Settings:
- Name: Windows 10 – Allow USB Drive
- Description: Allow USB Drive OMA URL Setting
- OMA-URI: ./Device/Vendor/MSFT/Policy/Config/System/AllowStorageCard
- Data type: Integer
- Value: 1
- Assignments: Assign this policy to an Entra security group which contains devices.

I’m looking for the correct way to implement the following:
* Block all removable storage devices except specific list of allowed USB removable drives
I looked at the ASR devicecontrol thing but I’m struggling with wildcards for the class (tried to do “block USBSTOR\*”) but that does not seem to work (error 65000)
What does work is enter “RemovableMediaDevices” in the “primary ID” field, that blocks the devices, however, I cannot override it then with a specific USB removable drive Hardware ID.
Any thoughts ?
Hi Vincent,
You can use “Allow installation of devices that match any of these Device IDs” policy in Intune to allow certain devices while still keeping the USB port blocked for all other devices. Please refer to below blog post for this. Let me know if it helps.
https://learn.microsoft.com/en-us/intune/intune-service/configuration/administrative-templates-restrict-usb