The TLS protocol is used to ensure privacy and data integrity when two applications communicate. SSL and TLS are both cryptographic protocols, but because SSL does not provide a sufficient level of security compared to TLS, SSL 2.0 and SSL 3.0 have been discontinued. TLS 1.0 was released in 1999, TLS 1.1 in 2006, TLS 1.2 in 2008, and TLS 1.3 in 2018.
If you’d like to learn more about these protocols, understand their differences, and explore security enhancements, you can visit the Protocol RFCs (Request for Comments) at the following links: TLS 1.0 RFC, TLS 1.1 RFC, TLS 1.2 RFC, and TLS 1.3 RFC.
Table of Contents
Options to Disable TLS 1.0/1.1 on Windows 10
I will show you below three ways to disable these weak protocols on Windows 10 Devices.
- By creating registry keys manually.
- By creating a group policy object (GPO) in Active Directory.
- By executing Powershell commands.
Option 1 – Create Registry Keys on Windows 10 devices
We’ll first go through the steps for TLS 1.0, and then we’ll cover the steps for TLS 1.1. Here they are:
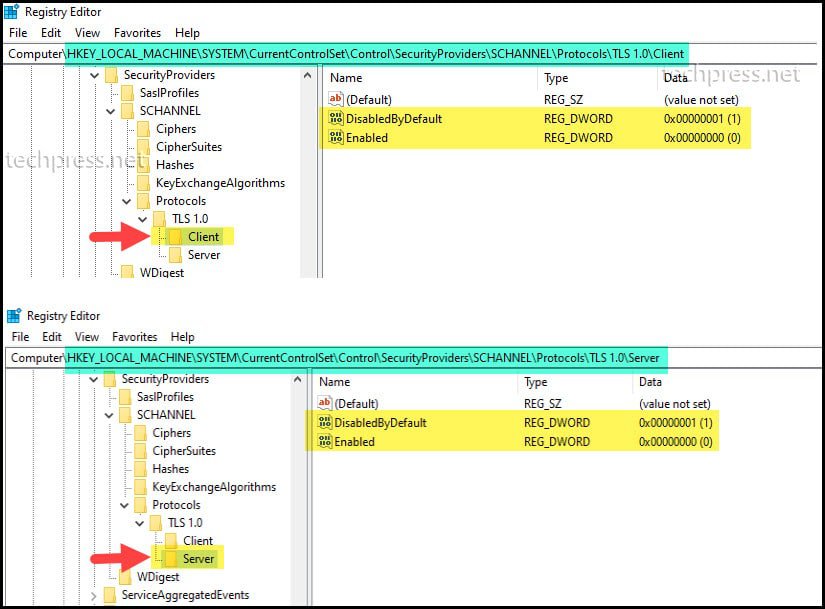
1. Create Registry Keys to Disable TLS 1.0
To create registry keys on Windows devices, follow the below steps:
- Press Windows key + R to open the Run dialog box.
- Type regedit and press Enter to open Registry Editor.
- Navigate to HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols
- Right-click on the “Protocols” folder and select “New” -> “Key“.
- Name the new folder “TLS 1.0” and create two subkeys under it: “Client” and “Server“
- Under both the “Client” and “Server” subkeys, create the following registry entries:
- Create a new DWORD registry entry named “DisabledByDefault” and set its value to “1“.
- Create a new DWORD registry entry named “Enabled” and set its value to “0“.
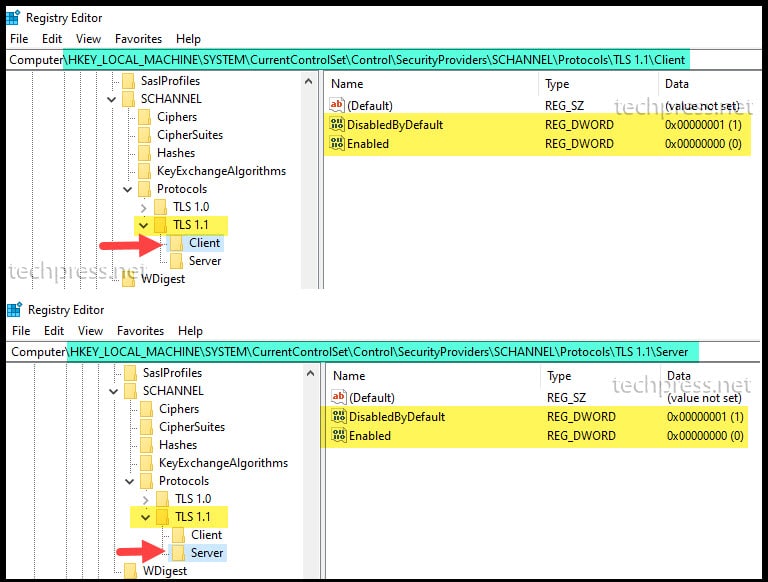
2. Create Registry Keys to Disable TLS 1.1
- Press Windows key + R to open the Run dialog box.
- Type regedit and press Enter to open Registry Editor.
- Navigate to HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols
- Right-click on the “Protocols” folder and select “New” -> “Key“.
- Name the new folder “TLS 1.1” and create two subkeys under it: “Client” and “Server“
- Under both the “Client” and “Server” subkeys, create the
- Create a new DWORD registry entry named “DisabledByDefault” and set its value to “1“.
- Create a new DWORD registry entry named “Enabled” and set its value to “0“.
Option 2 – Create a GPO to Disable TLS 1.0 and TLS 1.1
When you’re managing Windows 10 devices through Active Directory, there’s an easier way to deactivate TLS 1.0 and TLS 1.1. Instead of the tedious task of individually accessing each PC and creating registry entries, you can create a Group Policy Object (GPO) and link it Windows 10 Computers OU.
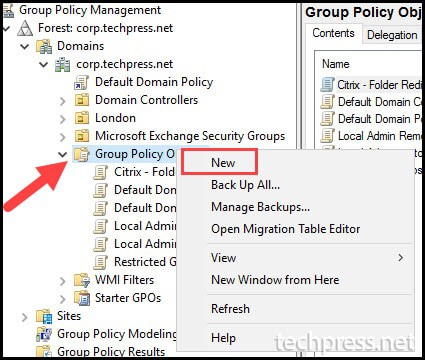
To create a GPO in Active Directory, follow these steps:
- Log in to a Domain controller as a Domain administrator.
- Press Windows key + R to open the Run dialog box.
- Type
gpmc.mscand press Enter to open Group Policy Management Console. - In the Group Policy Management Console, expand the “Group Policy Objects” folder. Right-click on it and choose “New“.
- Provide a Name of the GPO. For Example: Disable TLS 1.0 and TLS 1.1 Windows 10
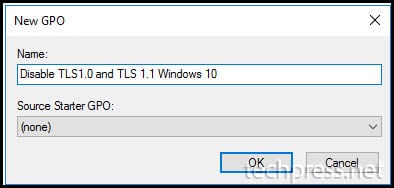
- Right-click on the “Disable TLS 1.0 and TLS 1.1 Windows 10” Group Policy and select “Edit“.
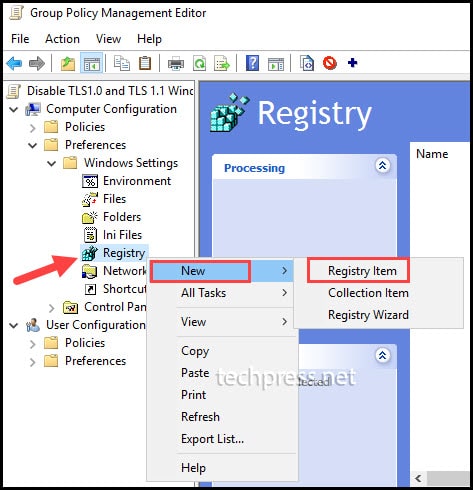
- Navigate to “Computer Configuration” -> “Preferences” -> “Windows Settings” -> “Registry“.
- Right-click on “Registry” and choose “New” -> “Registry Item“.
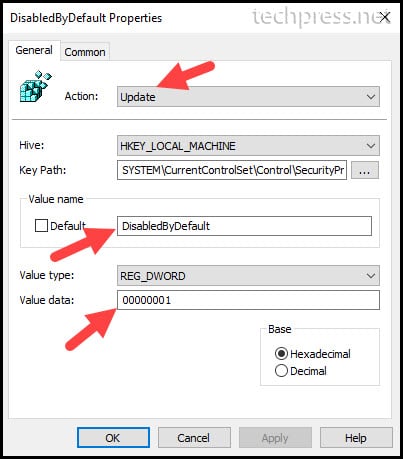
- Once you’ve clicked on “Registry Item” a window will appear where you can enter details about the registry item you want to create. You’ll need to provide the following information about the registry item:
- Action: Choose “Update” from the drop-down menu. Selecting “Update” will create the registry keys and entries if they are not already found on the target devices.
- Hive: Select HKEY_LOCAL_MACHINE
- Key Path: You can either browse to the registry path or provide the path directly.
- Value Name: We will be creating two registry entries per protocol. DisabledbyDefault and Enabled.
- Value type: Select REG_DWORD.
- Value type: 1 means the setting is Enabled and 0 means setting is Disabled.
- Repeat the process to create registry keys for each protocol. Here are the registry keys you can create for each protocol:
Registry Keys to disable TLS 1.0
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.0\Server] "Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.0\Server] "DisabledByDefault"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.0\Client] "Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.0\Client] "DisabledByDefault"=dword:00000001Registry Keys to disable TLS 1.1
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.1\Server] "Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.1\Server] "DisabledByDefault"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.1\Client] "Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.1\Client] "DisabledByDefault"=dword:00000001Registry Keys to disable SSL 2.0 [Recommended]
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 2.0\Server] "Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 2.0\Server] "DisabledByDefault"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 2.0\Client] "Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 2.0\Client] "DisabledByDefault"=dword:00000001Registry Keys to disable SSL 3.0 [Recommended]
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 3.0\Server] "Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 3.0\Server] "DisabledByDefault"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 3.0\Client] "Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 3.0\Client] "DisabledByDefault"=dword:00000001Registry Keys to Enable TLS 1.2 [Recommended]
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Server] "Enabled"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Server] "DisabledByDefault"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client] "Enabled"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client] "DisabledByDefault"=dword:00000000Registry Keys to Enable TLS 1.3 [Optional]
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.3\Server] "Enabled"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.3\Server] "DisabledByDefault"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.3\Client] "Enabled"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.3\Client] "DisabledByDefault"=dword:00000000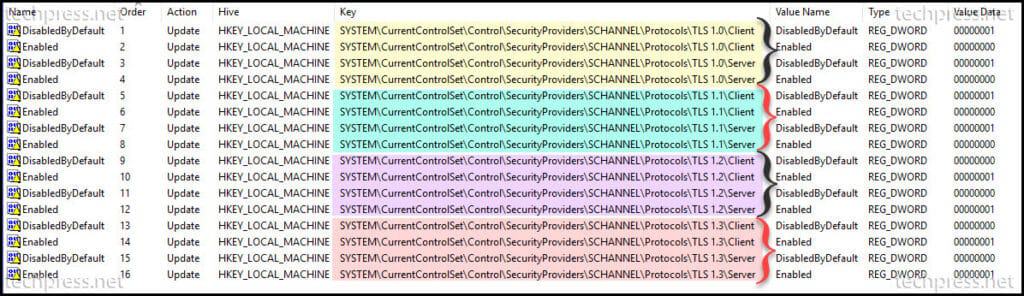
- After you’ve created all the registry items in the Group Policy Management Console for the “Disable TLS 1.0 and TLS 1.1 Windows 10” GPO, you can link the GPO to the Organizational Unit (OU) that contains the devices.
- It’s important to keep in mind that this Group Policy Object contains settings in the Computer Configuration, which will apply to the devices. A computer restart will be necessary to ensure that the registry entries are created and take effect.
Option 4 – Use Powershell to disable TLS 1.0 and TLS 1.1
Another way to disable TLS 1.0 and TLS 1.1 is by using Powershell cmdlet. This is especially time-saving when you need to disable these protocols on a large number of devices.
For more information on the PowerShell commands, you can refer to the blog post titled “How To Disable TLS 1.0 And TLS 1.1 Using PowerShell On Windows 10.”
More Information
1. Disable TLS 1.0 and TLS 1.1 for MSEdgeHTML/Internet Explorer
There are three ways to disable TLS 1.0 and TLS 1.1 for MSEdgeHTML/Internet Explorer, Please find below:
- Using Registry Editor on the Windows device.
- Using Group Policy Preferences (GPP)
- By creating a Group Policy Object in Active Directory.
1. Using Registry Editor to disable TLS 1.0 and TLS 1.1
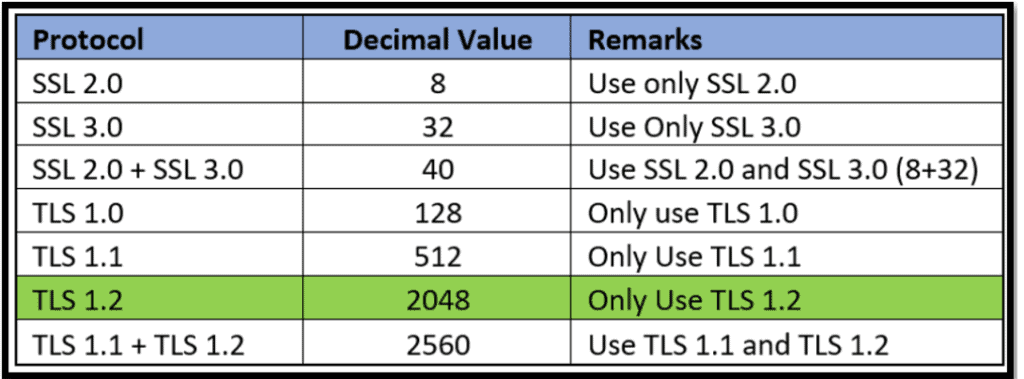
You can make use of the “SecureProtocols” registry entry located in both HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings and HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings to configure your preferred security protocols.
The “SecureProtocols” is a REG_DWORD value, and to enable or disable specific protocols, you can set it to the corresponding decimal value. If you want to enable only TLS 1.2, use the highlighted decimal value 2048.
2. Using Group Policy Preferences
You can create the above registry Items by using Group Policy Preferences to disable weak protocols.
3. Create a Group Policy Object in Active Directory
You can create a GPO in Active Directory to disable weak protocols.
- Go to Computer Configuration -> Policies -> Administrative Templates -> Windows Components -> Internet Explorer -> Internet Control Panel -> Advanced Page.
- Turn Off Encryption Support – Enable
- Secure Protocol Combinations -> Only use TLS 1.2
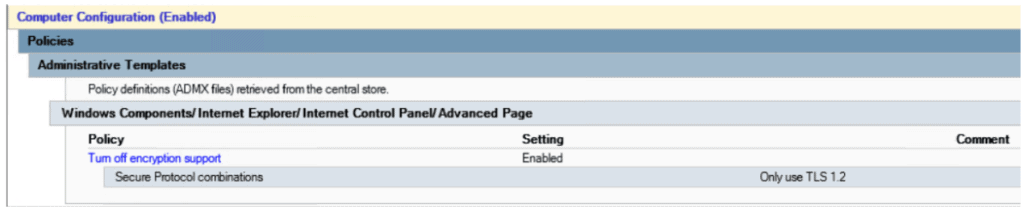
- Link the GPO to Computers OU.
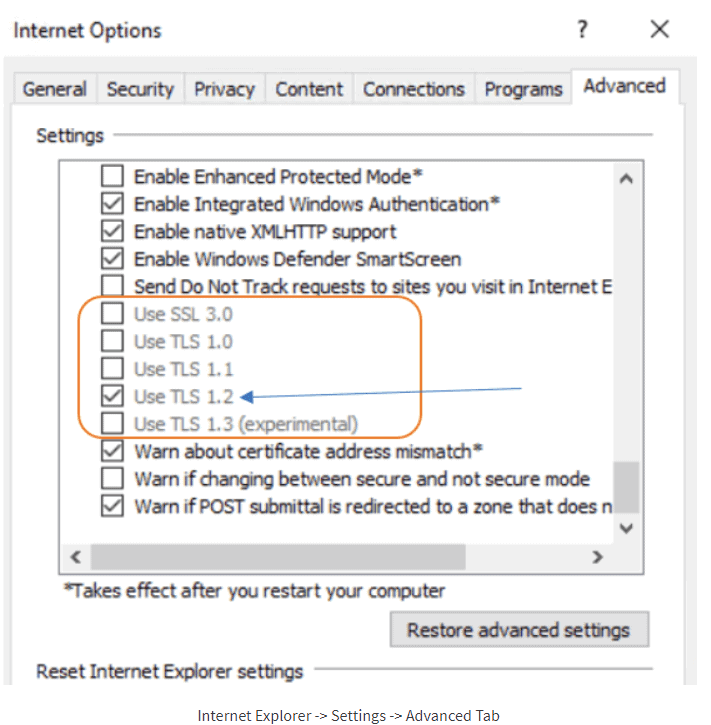
End-user Experience
- Once the Policies are applied, you can check and confirm in IE settings that the protocols are disabled.

Hi,
thanks a lot for this post!
Can you please confirm there is no mistake under:
Registry Keys to disable TLS 1.1
you have server and client registry for Enable key = 1
Correct. Enable should be 0 and DisabledByDefault should be 1. Updated the post. Thanks.